Hertzbleed – A new side-channel power analysis attack
| 23-06-2022 | By Robin Mitchell
A new vulnerability has been discovered in modern Intel and AMD CPUs that allows an attacker to obtain secrete keys by analysing the power consumption from the target CPU. Why are side-channel attacks problematic, how does Hertzbleed work, and is it a real threat?
Why are side-channel attacks problematic?
When it comes to hacking a device, there are many routes an attacker can use. For example, a brute force attack on a password involves trying every possible password combination until the right one is found. This can be mitigated with long passwords and a combination of letters and symbols, but hackers continue to use this method as humans are extremely predictable with passwords (often referred to as a dictionary attack).
Other attacks often try to look for exploits and weaknesses in a system that are unknown to the designers. For example, poor SSL implementation (such as Heartbleed) could allow an attacker access to private memory if messages being sent are mismatched to the expected message length number. This type of exploit can be fixed by updating software libraries to include protection methods to patch bugs.
But one type of attack, known as side-channel attacks, is particularly problematic as they are designed to outright avoid protection systems and detection software by using a side-channel. For example, a computer may be fitted with strong anti-virus and firewalls, but if the USB port to the system is left entirely exposed, then a hacker could connect an external keyboard, reboot the system, and enter the BIOS whereby full privileges are given.
Side-channel attacks can also attack software components whereby some system service generally seen as benign could accidentally expose a secure system component. Fundamentally, a side-channel attack aims to find an alternative path to a goal that bypasses any systems put in place to prevent access.
Defending against a side-channel attack presents challenges to engineers as they are not so easily fixed. In the case of hardware, it may be outright impossible to prevent a side-channel attack, and software side-channel attacks can be difficult to prevent if components being exploited are not controlled by the engineer (i.e., third-party software).
How does Hertzbleed work?
Recently, researchers have discovered a new side-channel attack that allows an attacker to extract cryptographic keys used by SIIKE, a post-quantum encryption system. While the paper that describes the attack is highly complex, the fundamentals can be broken down into the following points:
- CPUs that use power-scaling and dynamic frequency changes do so depending on the workload
- A piece of code that takes n cycles does not take n time due to dynamic frequency scaling
- An encryption method that processes large amounts of data for each bit is vulnerable
Modern CPUs are designed to try and save power whenever idle and maximise their power usage when under heavy load. Furthermore, this amount of scaling depends on the size of data being processed, and the researchers discovered that minute changes in individual bits can be detected through external power monitoring and repeated identical calculations. The use of frequency scaling also changes the time taken for the processor to complete an operation, and this change in time can also indicate the value of a bit.
If this ability to detect changes in bits through repeated calculation is possible, it goes without saying that it would be possible to determine each bit of a number if an energy-intensive task goes through each bit of a private number and performs a large number of calculations per bit. This is where the researchers turned their attention to SIKE, a post-quantum encryption system.
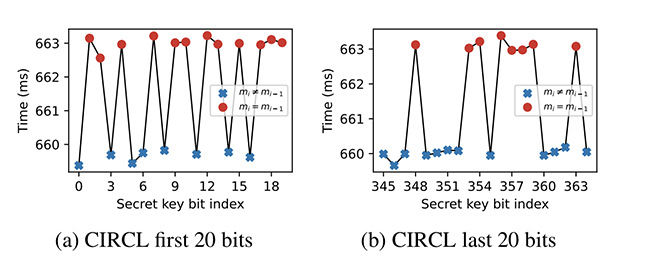
It turns out that SIKE performs a large number of calculations on each bit of a secrete key, and by repeatedly sending the same cyphertext to the target machine and timing the round trip, the value of the secrete key can be extracted.
Is Hertzbleed a serious threat?
One concern that Hertzbleed presents is that it was able to extract the key to a quantum-safe encryption method. Considering that these encryptions are being introduced to protect against future quantum computers, the use of a timing attack to extract the key shows that they require more work.
However, it should also be stated that the attack demonstrated by the researchers is only practical in a laboratory environment and not something that could be done easily from a remote location with no physical access to the server. But it does bring to light how side-channel attacks can be used in the most unusual ways to successfully recover data without giving the system under attack any indication of an attack.
It would seem that the best way to protect against such an attack is to either disable frequency scaling so that the CPU is continuously operating at maximum power, change the software so that repeated operations are not as obvious through power monitoring, or introduce an aspect of randomness to operations requiring independent operations to process a request, then the order of operations could be randomised.

