Cheap IoT Technology Paves the Way for a Global Hackathon
| 24-10-2019 | By Paul Whytock
By the year 2025 there will be approximately 28 billion Internet-of-Things (IoT) devices in operation worldwide and this is a massive security accident just waiting to happen.
In fact, that’s wrong, it's already happening and that’s because a vast number of IoT gadgets aimed at unwitting consumers are a dream opportunity for hackers.
Why is this? The primary reason is companies want to make their IoT goodies price attractive and this is totally understandable, it’s a hugely competitive market out there.
The problem is in an attempt to encourage the cash out of the consumers’ wallets manufacturing costs are often cut and unfortunately, one product area that is often used by corporate bean-counters to cut costs relates to data security.
What the penny-pinchers dislike is twofold. Firstly good product security doesn't come cheap and even when a suitable investment is made in state-of-the-art security those systems are quickly superseded by the need for newer and better security in order to keep up with the incorrigible inventiveness of hackers
So concerned by this IoT security sloppiness was the Japanese government it actually authorised a campaign whereby it hacked into peoples IoT devices to gain a better understanding of security weaknesses and how to resolve them
Japan’s National Institute of Information Communications Technology used default passwords to break into Japanese consumers’ IoT devices. Needless to say, the campaign caused public outrage and not a lot of valuable security-related info was forthcoming.
The plain fact is that electronic data security costs money but it should be at the heart of IoT design; a part of product DeoxyriboNucleic Acid.
Enter stage left the manufacturing concept of provisioning, a way in which electronic devices can have code embedded in them without the possible security intervention of dishonest or incapable humans during their production process.
So if we take a sensor for example that is being integrated into an electronic product, provisioning means it is configured and installed at the site of manufacture automatically. It will upload its own data. Humans are not involved and codes remain totally secret.
There is no doubt that device provisioning is a very complex and effective security feature and a fundamental element of it involves the process of attaching a certificate to the device identity.
Device identity is very similar to user identity but is used to specifically identify a single device. It's important because with operational facilities like push notification it is a very good thing to have knowledge of which device you are sending the notification to. And for server operators, you need to know how many devices are using your server.
Returning to the security implications of having humans involved in device provisioning it is a fundamental imperative that the provisioning system allows device makers to remotely monitor and control the related manufacturing process without actually having to be present at the production location.
Crazy IoT Hacks
Presently the security inadequacies of many IoT devices means there is now a history of hacks that involve anything from “intelligent” toy dolls through to expensive cars, through to house security cameras that link to iPhones and central heating control systems.

In fact the list is way too long to go into here but here's one example that left citizens of Finland feeling very chilly for a week.
Heating thermostats are an easy target for mischievous hackers and an apartment building in Finland was attacked which left residents without heat for a week. And don’t think your smart TV is immune. Internet-enabled TVs can be hacked and data harvested, channels can be changed and inappropriate material shown.
Plenty is happening on provisioning and the struggle to make IoT devices more secure. One development from semiconductor company Microchip will simplify the creation of hardware-enabled IoT security by providing provisioned solutions for low, mid and high-volume applications
It says that hardware-based security is the only way to protect secret keys from physical attacks but as mentioned earlier there are substantial costs involved in ensuring a high level of security in each device.
With companies producing anywhere from hundreds to millions of connected devices per year around the globe, scalability of architecture can be a major barrier to deployments.
What Microchip thinks is manufacturers typically have only been able to support configuring and provisioning for high-volume orders, leaving companies with low to mid-sized deployments with under-specified options.
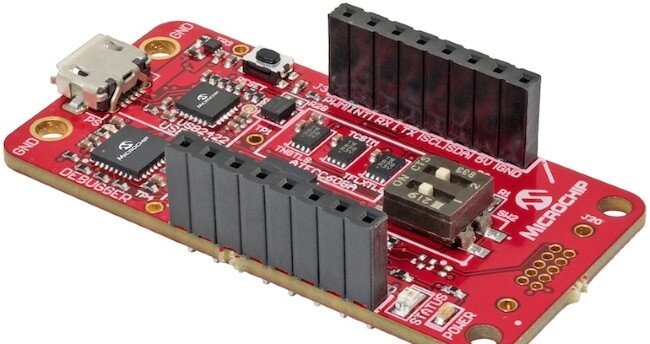
To address this need in the mass market, Microchip Technology developed what it claims is the industry’s first pre-provisioned solution that provides secure key storage for low, mid and high-volume device deployments using the ATECC608A secure element.
Microchip’s provisioning facility is named Trust Platform and consists of a three-tiers which let developers choose a platform suitable for their individual designs.
Claiming it to be the first solution to create customer-ready secure authentication for the mass market, the first tier provides zero-touch pre-provisioned secure elements on production runs of only 10 units. Device credentials are pre-programmed, shipped and secured inside ATECC608A for automated cloud or LoRaWAN authentication on-boarding. In parallel, corresponding certificates and public keys are delivered in a manifest file which is available online via Microchip’s e-commerce store and certain distribution partners.
In addition to saving up to several months of development time, the solution is claimed to simplify provisioning logistics, making it easy for mass-market customers to secure and manage edge devices without the overhead cost of third-party provisioning services or certificate authorities.
The second tier in the provisioning program provides flexibility to use the customer’s certificate authority of choice while still benefiting from pre-configured use cases. These use cases include baseline security measures such as Transport Layer Security hardened authentication for connecting to any IP-based network using any certificate chain, LoRaWAN authentication, secure boot, Over-the-Air updates, IP protection, user data protection and key rotation.
Finally, Microchip worked with Amazon Web Services (AWS) to enable a simplified onboarding process into AWS IoT services for products designed with the Microchip system.
The ATECC608A provides Common Criteria Joint Interpretation Library secure key storage. With the hardware-based root of trust storage and cryptographic countermeasures, the system protects against a number of known physical attacks. Microchip’s secure manufacturing facilities safely provision keys, ensuring that keys are never exposed to any party during provisioning or the lifetime of the device.
It’s fair to say that anything which enhances IoT security is very desirable and this fact is made clear by a recent report from the security company Gemalto when it surveyed nearly 1000 companies that make and use IoT technology and found that 48% of companies don’t have mechanisms in place to detect if any of their devices are hacked or not.
This is worrying in itself but also seems self-destructive for many IoT companies when it's considered that many of their customers would think effective product security a very strong selling point that could be the deal-making differential between them and rival IoT companies.

